What is Fraud?
Fraud occurs when a person misleads another person by word, actions, or document/s for that person to improperly benefit the person engaging in the fraudulent activity or to another person.
It is formally defined by the Commonwealth Fraud Prevention Centre as an action that dishonestly obtaining a benefit, or causing a loss, by deception or other means.
Benefit can be money, property, goods, shares, tickets – anything of value to a person.
A person must believe the representation and act on it to his/her benefit or detriment or to the benefit/detriment of a third party.
The Association of Certified Examiners (ACFE) recently estimated organisations would lose at least 5% of their revenue to fraud every year.
What drives a Fraudster?
In 1953, American criminologist Donald Cressy developed what is now known as the “Fraud Triangle” theory. He proposed three factors contribute to fraud and unethical behaviour in an organisation.
These were: Pressure, Opportunity, and Rationalisation.
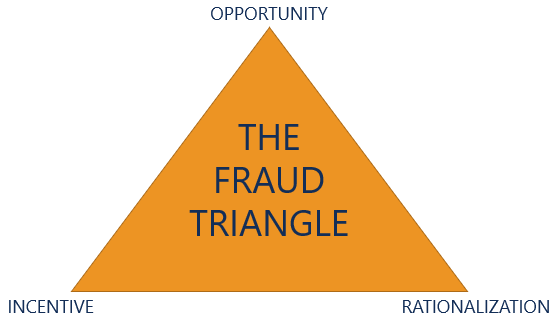
Pressure
There is pressure on an individual causing him/her to commit the act. This pressure may not be readily identifiable but it will exist. It may include such things as lack of money, gambling debts, alcohol or drug addiction or other financial pressures (medical, education etc.). It is important to appreciate the trigger can also include pressure on friends or relations.
Greed linked to perceived injustice is also a trigger for fraud. The offender believes the company is not recognising his/her qualities, not paying enough, not promoting, or mistreating him/her.
Opportunity
There is an opportunity to commit the crime. This can be a temporary opportunity to commit the crime with little likelihood of being caught. It can also be a situation where a person in a particular position (accountant, asset manager, purchasing officer etc.) identifies lack of controls and exploits them. Generally, there will be a “testing of the waters” moment to see if their actions are noticed. The fraudulent act then increases as s/he believes they are not likely to be caught.
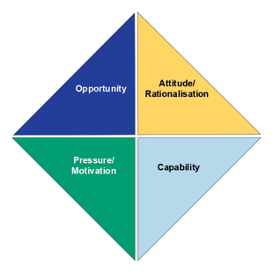
“Opportunity” is also linked to the ability of the offender to commit the crime. Are they in a position to manipulate data, change records, produce false documentation? The capability of offender is sometimes incorporated into the fraud triangle theory to form a 4th category leading to the “Fraud Diamond” theory.
The offender can commit the fraud either through position/s (accounts) within the company or the knowledge (ability to manipulate computer data) of how to commit the crime.
Rationalisation
“I deserve this, I have worked hard for this company, I will pay it back, I only need a small amount”. These are all excuses flowing through the mind of the offender. There is “justification” for their actions.
Escalation of offending
The offender may “test” the system to see if anyone identifies the fraud. Generally, this is a small amount and the offender has an “excuse” ready if it is detected.
How do I detect fraud in my business?

Employees
You need to be vigilant for various changes in business practices and/or personal attitudes of key personnel.
These include, but are not necessarily limited to:
- Person in key position (accountant, purchasing officer etc) refusing to share duties or to take leave.
- Person in key position declining promotion or transfer – “I like this position. I am happy here”.
- Person works longer hours than normal – last out (provides opportunity to change records without scrutiny).
- A unwarranted change in suppliers at request of purchasing officer.
- A refusal or reluctance to accept oversight measures (second signature, more transparency in purchasing and so on).
- Skipping approval steps and/or not having segregation of duties in the procurement process.
- Living a lifestyle not equitable to their renumeration, trips, gifts to other employees, expensive vehicles, and other obvious signs of wealth.
- Providing excuses such as “death of a relative” to explain this increase in wealth.
- Failing to keep accurate records including receipts for expenses.
- Bullying colleagues especially when a person tries to review their actions.
- Seeking access to areas when not entitled to access – this may be physical areas (store rooms, warehouse etc) or accessing areas within the accounting process (trying to change records!).
- Ongoing evidence of shortage of cash, financial hardship.
- Consistently seeking loans from other employees or advances on salary.
- Addiction problems – drugs, gambling etc. Note this may be a relative or friend seeking help.
- Significant personal stress linked to underlying need for increased funds.
- A strong sense of entitlement – “I am the best thing for this company”. I deserve recognition.
- Unhappy with employer or supervisors – rationalisation for actions.
- Unusual “shrinkage” of inventory
- Key documents not completed or are missing
- Unusual payment including variations and, multiple actual or similar payments to same vendor/contractor
- Creditors contacting and/or attending work site seeking a person.
- Employee previously faced internal discipline (80% from ACFE survey).
High risk activities
These areas are linked to fraud within the company:
- Management of vendors and accounts payable
- Handling of cash payments
- Reimbursement of travel and ancillary payments
- Management of contracts – external providers, consultants, or projects
- Privileged access to financial and/or purchasing records (Administrator status)
- Procurement
- Payment of invoices, receipt of goods, ordering of goods.
- Access to payroll and other employee data
- Fail to comply with approved vendor list or panel suppliers
How do I prevent fraud in my business?

You need a structured approach. There is a concept known as the “fraud control cycle”. This comprises of three distinct areas to consider when developing a fraud mitigation model.
The first area is prevention. The policies and practices should provide guidance in reduction and elimination of fraud across your business. The 2020 ACFE Report to the Nations highlighted a lack of internal controls contributed to 1/3rd of reported frauds.
However, there is always the potential for fraud to occur despite strong preventive measures. The second phase of the cycle is to develop practices linked to red flags appropriate for your industry. This will enable you to discover fraud before it causes too much harm to your company’s financial and reputational standing in the community.
The ACFE Report indicated a typical fraud case lasts 14 months before detection and causes a loss of A$11380 a month – Approximately A$159,000.
The final phase in the cycle is “what am I going to do” if fraud is identified? The is the response phase. There should be a detailed response on what to do. How do I retain evidence? Whom do I approach? Do I commence an investigation? Do I stand the person down? Should I tell the police?
The monitoring of preventive measures linked with a documented approach to reporting will assist in controlling opportunities for fraud in your business.
Fraud Prevention
It is important to recognise the significance of preventive measures within your business.
One way to approach this is to consider the four points of the “fraud diamond”. These are: Pressure, opportunity, capability, and rationalisation.
Pressure
It may be difficult to assist with personal issues leading to “pressure” on the employee but you should encourage employees to seek assistance. An “open door” policy allows employees to discuss personal issues with no fear of repercussion. Referral facilities should be identified and this information provided to employees. An employee assistance program (EAP) is an excellent way to assist employees in times of stress.
Relieving this pressure can reduce to need to commit fraud.
Opportunity
Implementing policies, practices, and set procedures with cross checking reduces the opportunity to commit fraud.
ACCA can assist by assessing your security and fraud mitigation efforts. This assessment will assist you in developing and strengthening your fraud shield to protect you from financial and reputational damages from fraud.
Capability
You need to closely monitor areas where a person has access to your records – s/he can change financial records. You also have to demand segregation of duties. A single person should not approve a purchase, acknowledge receipt of goods or services, authorise payment, and update the asset register.
Also insist staff in key areas take leave – a red flag is a reluctance of offenders to allow other persons access to their operating areas.
Rationalisation
You must have a “zero tolerance” approach to fraud. If a person is identified then seek police assistance, dismiss the person, do not provide any form of recommendation for future employment.
Ensure all employees know the fraud prevention policy including zero tolerance. Provide regular training for employees and suppliers. If a supplier is identified as participating then refuse to deal with the supplier. ACFE report indicated formal reporting processes resulted in a 56% greater likelihood of reports compared to 37% where there was no formal process.
Ensure you have a reporting mechanism to allow employees and suppliers to provide information on suspected fraudulent activity. This can be a hotline or similar reporting process. ACFE report highlighted 43% of fraud schemes were detected through tip-offs. Half of these tips were from employees. It also highlighted a telephone hotline and/or email were each used by whistle-blowers.
Basic preventative measures
Research indicates there are basic preventive measures for any business.
Basic preventative measures
Research indicates there are basic preventive measures for any business.
1. A code of conduct.
You need a code of conduct or a similar document to clearly outline expectations of behaviour within the business.
This need not be a lengthy document but should address the key areas of expected behaviour (respect, no bullying, no sexual harassment, compliance with policies etc).
The code of conduct should stress the need for integrity in all dealings with other employees, suppliers, customers, and the general community.
2. Policies/Procedures
These complement the code of conduct. They address specific areas such as procurement, fraud and corruption prevention, reporting of identified infringements, and other work practices. The latter may include specific instructions relating to work practices such as reimbursement of expenses, allowances, segregation of duties.
This should also include a “gifts and benefits” policy. Employees and suppliers need guidelines on what is regarded as a gift or a benefit.
3. Training
It is pointless to have a code of conduct and other documentation if the employees and suppliers do not know about them. This means all new employees and suppliers must participate in training. This would occur at induction and throughout the year. There should be at least one training session for each employee and supplier (signed off as attending) per year.
4. Conflict of interest
Maintain a conflict-of-interest register. This is essential for personnel involved in procurement. A conflict does not necessarily mean there can be no interaction. It means the conflict must be “managed” to ensure integrity.
If the conflict cannot be transparently managed then the employee must not be involved.
5. Due Diligence
You must conduct due diligence on all new employees – make sure the information provided is correct. This is very important for persons in key positions (management, accounting, purchasing). Verify educational qualifications, insist on written recommendations, cross check any recommendations (social media is a great source). Make sure all certifications (CPA etc) are current.
Due diligence also extends to suppliers especially those contracted through a third-party agency. You need to verify office and factory addresses, banking details, location of banks, any other firms (where possible) conducting business with the supplier.
Regular cross referencing of supplier details (bank, business, and personnel) against employee details is also important.
Audit of employee records will identify ghost employees left on payroll. You should also have a process to identify and verify any changes of banking details for employees and suppliers.
6. Segregation of duties
This is essential. You cannot have the same person approving a supplier, identifying a business need, authorising purchase, signing off on receipt of goods/service provided, authorising payment of invoice, and updating (where appropriate) the asset register. A failure to do this guarantees fraud will occur.
Purchasing officers must complete a conflict-of-interest declaration relating to all suppliers. This should extend to the family and/or associates of the supplier.
7. Rotation of staff in key areas
This may be difficult but the rotation of personnel ensures no one is in a position for enough time to create a fraudulent scheme. It can also assist in identifying schemes because the new person is likely to identify anomalies in practices.
8. Ad-hoc audits
Conduct ad-hoc audits to review payments, bank account details, employee records (ghost employees), cash handling.
If you are a small business owner and need help with this, visit our ‘Small Business Theft and Fraud‘ page to learn how we can help.
Fraud Cases
$12 million Fraud

Glenda Burgess was a “trusted account manager” for Adelaide Brighton Cement. She was found guilty of 18 offences between August 2009 and September 2017.
The investigation identified no she derived no apparent benefit from the $12 million taken from the firm. A customer (Concrete Supply) benefited from her actions as they did not have to pay $12 million for goods supplied.
She created false entries into the company’s ledger to favour Concrete Supply. The records indicated the customer received $32 million of supply but only paid around $20 million. She hid the underpayments by creating a false debtors report. She also increased the credit standing for Concrete Supply without approval and transferred debt away from the company to another customer. She allocated payments from other customers to benefit outstanding debt of Concrete Supply.
Ms Burgess showed no contrition or remorse for her actions. Her actions caused substantial damage to the business reputation of Adelaide Brighton Cement. They lost several long-term customers.
Court records indicates she stole from a former employee.
She was gaoled for seven (7) years.
Comment
She remained in her position for at least eight (8) years. There was no apparent regular audit of invoices and supplier relationships. She had prior history of theft (lack of due diligence).
Adelaide Brighton Cement received adverse media exposure because of her actions. This was to their detriment in the market place.
Fraud Diamond – She had the opportunity, and she had the capability. She did not comment on her actions, she provided no reasons for her conduct. This would indicate she rationalised her behaviour. There was no indication of what pressure was applied or what pressure she was under to commit the offences.
Couple conned out of $1 million through email scam

This is becoming a common scam. The Northern Beaches couple were purchasing a home. They received an email allegedly from their solicitor for payment of $1.1 million to finalise the purchase of the home.
The email provided details of a bank account for payment. The couple went to the Commonwealth Bank to transfer the funds. They contacted the solicitor to advise him of the transfer.
He immediately told him to contact the bank as he did not send the email. They did so and, luckily, the bank froze the funds. The couple eventually got their money back.
The email appeared legitimate as it had all the contact details of the solicitor and was an exact copy of previous emails – the bank details were false.
Ex Surf Life Saving boss jailed for fraud.

Matthew Hanks was the General Manager for Surf Lifesaving NSW. He was gaoled for three years and three months for defrauding the charity of $1.8 million between 2007 and 2016.
He used various methods to commit the fraud. These included secretly selling SLS NSW vehicles to himself at cost then on selling to private buyers at a higher price. He kept the difference.
He also commenced a company called “See Hear Speak”. This was a printing firm. He contracted SLS NSW business to this company. He then sub-contracted the business to other firms at a cheaper rate. He invoiced SLS NSW for the full amount and kept the difference. He did not declare a conflict of interest.
In 2012, he changed the details on a grant cheque for $121,000 from the NSW government for a new clubhouse at Port Macquarie. He put the cheque into his personal account. No one noticed this had occurred.
Mr Hanks indicated the lack of awareness of this transaction indicated to him SLS NSW was not managing him appropriately. He was immune from oversight. It was “almost too easy” to offend.
Mr Hanks used the money to pay for a yacht and mortgage debts.
He paid SLS NSW approximately $1.2 million before sentencing. He was sentenced to three years and three months.
Comment
He was a senior manager. There was no apparent independent oversight of his activities. The theft of the $121,000 cheque in 2012 should have been readily identified.
No due diligence around the supplier “See Hear Speak”. This would have identified his association with the supplier. No oversight on the purchase and sale of vehicles. Where was the money for the sale of these vehicles.
An “asset register” within the organisation would have identified these discrepancies.
Trust – a major factor in fraud. He was a senior manager in a position of authority. There was no apparent external oversight of his activities.
ACFE report indicated financial fraud schemes were the least common but the costliest with a median loss of A$1.3 million.
Fraud Diamond – He had the opportunity, and the capability. He committed the offences because “he could”. He rationalised his activities by commenting it was “almost too easy” to offend.
There was no information of “pressure”. He became too greedy because no one challenged him
Townsville woman jailed for stealing more than $50K from employer

Ms Tuitahi used a company credit card 704 times over 18 months charging $50,990 in false purchases.
She used the card for personal purchases including groceries, phone accounts and alcohol. Most transactions were under $100. She disguised the transactions on the monthly reports.
He role as inventory control officer provided access to the company credit card. She commenced offending by initially using the card on two small transactions in one month. There were no challenges to the use so she increased her offending to over 40 transactions each month.
Her defence argued the items were for living expenses. She was helping support her parents and other family members on a small wage.
Her manager was dismissed from the firm because he did not identify the fraudulent activities.
She was sentenced to two and half years in custody suspended after she served six months.
Comment
The classic start small, not challenged so expand activities. No appropriate oversight. Manager dismissed for failing to identify fraud.
Fraud Diamond
Pressure: Allegedly supporting family. Opportunity – she had access to the card. There was no apparent reconciliation of expenditure. She exploited internal weaknesses. Capability – she had access to the accounts so could disguise her activities as transactions on monthly reports. Rationalisation – not large amounts, needed to support parents and other family members. Was not being paid enough.